- 环境 traefik 2.2+,k8s 1.8+
- 需求:自动获得证书,使用aliyun dns方式获证书,暴露给外网访问
- 参考官方网站:https://docs.traefik.io/user-guides/crd-acme/
- 首先安装helm, k8s的一个类似yum包管理器。 参考https://helm.sh/docs/intro/install/
- Download your desired version
- Unpack it (
tar -zxvf helm-v3.0.0-linux-amd64.tar.gz) - Find the
helmbinary in the unpacked directory, and move it to its desired destination (mv linux-amd64/helm /usr/local/bin/helm)
- traefik有二种模式: 1. 使用 Traefik CRD 配置路由规则(IngressRoute),2. 使用 Kubernetes Ingress 配置路由规则(Ingress)
- IngressRoute Definition,拷贝 https://docs.traefik.io/user-guides/crd-acme/#ingressroute-definition 里面的yaml文件并应用
kubectl apply -f ingress-route-definition.yaml
- 创建ServiceSecret
#说明1:secret的数据需要base64编码(https://kubernetes.io/zh/docs/concepts/configuration/secret/)
echo -n 'admin' | base64
#说明2:增加一个存储(根据实际情况修改),验证通过的证书我们这里存到/etc/acme/acme.json文件中,我们一定要将这个文件持久化,否则每次 Traefik 重建后就需要重新认证
#说明3:Service直接暴露了端口使用(NodePort),未使用官方文档的kubectl port-forward
#说明4:- --providers.kubernetesingress
# - --providers.kubernetescrd
# 导出二种支持的模式ingress, ingress-route
#说明5:dashboard不直接导出,保护资源,后面会通过https+basic auth方式查看
#traefik.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: traefik-ingress-controller
---
apiVersion: v1
kind: Secret
metadata:
name: aliyun-secret
data:
ALICLOUD_ACCESS_KEY: your_key_base64
ALICLOUD_SECRET_KEY: your_secret_base64
ALICLOUD_REGION_ID: your_region_base64
---
apiVersion: v1
kind: PersistentVolumeClaim
metadata:
name: traefik-acme-cephfs-pvc
spec:
accessModes:
- ReadWriteMany
resources:
requests:
storage: 1Gi
storageClassName: rook-cephfs
---
kind: Deployment
apiVersion: apps/v1
metadata:
name: traefik
labels:
app: traefik
spec:
replicas: 1
selector:
matchLabels:
app: traefik
template:
metadata:
labels:
app: traefik
spec:
serviceAccountName: traefik-ingress-controller
volumes:
- name: acme-store
persistentVolumeClaim:
claimName: traefik-acme-cephfs-pvc
readOnly: false
containers:
- name: traefik
image: traefik:v2.2
args:
- --api.insecure
- --log.level=INFO
- --accesslog
- --entrypoints.web.Address=:8000
- --entrypoints.websecure.Address=:4443
- --providers.kubernetesingress
- --providers.kubernetescrd
- --certificatesresolvers.aliyun.acme.dnschallenge.provider=alidns
- --certificatesresolvers.aliyun.acme.email=your_email@qq.com
- --certificatesresolvers.aliyun.acme.storage=/etc/acme/acme.json
envFrom:
- secretRef:
name: aliyun-secret
volumeMounts:
- name: acme-store
mountPath: /etc/acme
ports:
- name: web
containerPort: 80
- name: websecure
containerPort: 4443
- name: admin
containerPort: 8080
---
apiVersion: v1
kind: Service
metadata:
name: traefik
spec:
type: NodePort
selector:
app: traefik
ports:
- protocol: TCP
port: 80
name: web
targetPort: 80
nodePort: 31001
- protocol: TCP
port: 4443
name: websecure
targetPort: 4443
nodePort: 31000
---
apiVersion: v1
kind: Service
metadata:
name: traefik-dashboard
spec:
selector:
app: traefik
ports:
- protocol: TCP
port: 8080
name: admin
targetPort: 8080
- 模式一:在实际应用中创建Ingress
kind: Ingress
apiVersion: networking.k8s.io/v1beta1
metadata:
name: myingress
annotations:
traefik.ingress.kubernetes.io/router.tls: "true"
traefik.ingress.kubernetes.io/router.entrypoints: websecure
traefik.ingress.kubernetes.io/router.tls.certresolver: aliyun
traefik.ingress.kubernetes.io/router.tls.domains.0.main: your_domain.com
spec:
rules:
- host: your_domain.com
http:
paths:
- path: /bar
backend:
serviceName: whoami
servicePort: 80
- path: /foo
backend:
serviceName: whoami
servicePort: 80
- 模式二:IngressRoute
apiVersion: traefik.containo.us/v1alpha1 kind: IngressRoute metadata: name: ingressi-route-wqtls namespace: default spec: entryPoints: - websecure routes: - match: Host(`your_domain.com`) kind: Rule services: - name: whoami port: 80 tls: certResolver: aliyun domains: - main: "your_domain.com" - 解析域名并可以访问了https://your_domain.com:31000/bar

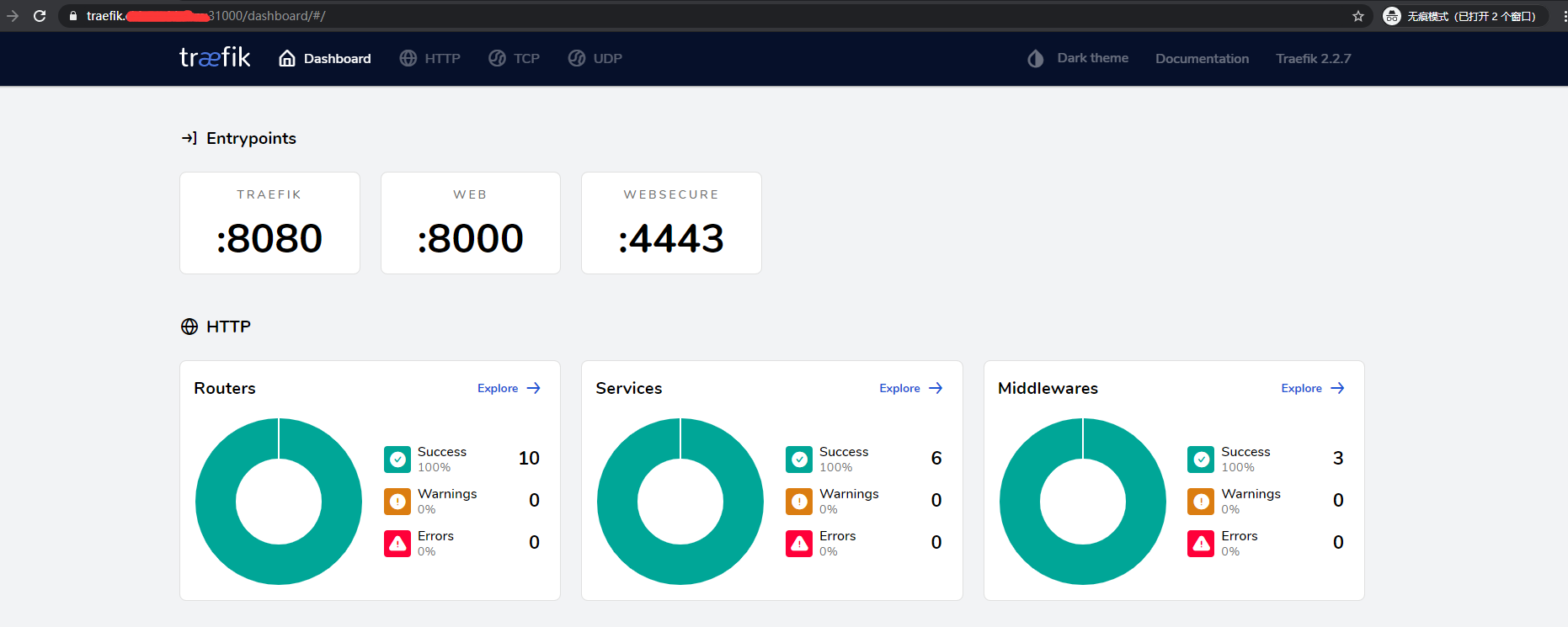
- dashboard安全使用。参考: https://docs.traefik.io/operations/dashboard/
#通过以下命令生成(在线生成https://tool.oschina.net/htpasswd)帐号密码 #并替换Secret中的users sudo apt install apache2-utils echo $(htpasswd -nb admin gJv4EAfuXp5vFJ8)
apiVersion: v1
kind: Secret
metadata:
name: traefik-dashboard-auth-secret
namespace: default
type: Opaque
stringData:
users: admin:$apr1$tQ1iFwRf$8SvGrGQcBT.RdZS73ULXH1
---
apiVersion: traefik.containo.us/v1alpha1
kind: Middleware
metadata:
name: traefik-dashboard-auth
namespace: default
spec:
basicAuth:
secret: traefik-dashboard-auth-secret
---
apiVersion: traefik.containo.us/v1alpha1
kind: IngressRoute
metadata:
name: traefik-dashboard
namespace: default
spec:
entryPoints:
- websecure
routes:
- kind: Rule
match: Host(`traefik.your_domain.com`) && (PathPrefix(`/dashboard`) || PathPrefix(`/api`))
services:
- kind: TraefikService
name: api@internal
middlewares:
- name: traefik-dashboard-auth
tls:
certResolver: aliyun
domains:
- main: "traefik.your_domain.com"
来源:oschina
链接:https://my.oschina.net/u/160697/blog/4437939
